The Limitations of Limiting Mobile Device Location Data Exposure
The National Security Agency (NSA) recently provided guidance on limiting mobile device location data exposure for National Security System (NSS) / Department of Defense (DoD) users. As noted by The New York Times last December, the value of location data to a foreign adversary can be immense as it may be used to determine the number of users in a place of interest, user and supply movements, daily routines of users and organizations, and otherwise unknown associations between users and locations.
In their guidance, the NSA notes that apps and system services may determine location data via cellular, Wi-Fi, GPS, or Bluetooth, which makes limiting location data exposure challenging. The NSA’s recommendations to minimize location data exposure include:
- Disabling location access on the device,
- Disabling Bluetooth and Wi-Fi when these are not needed,
- Use Airplane Mode when the device is not in use (ensure Bluetooth and Wi-Fi are disabled when Airplane Mode is engaged).
- Periodically resetting the device Ad tracking ID,
- Limiting the use of everyday consumer apps including maps, compasses, traffic apps, and fitness apps, and
- Leaving devices at “home” for missions performed at sensitive locations.
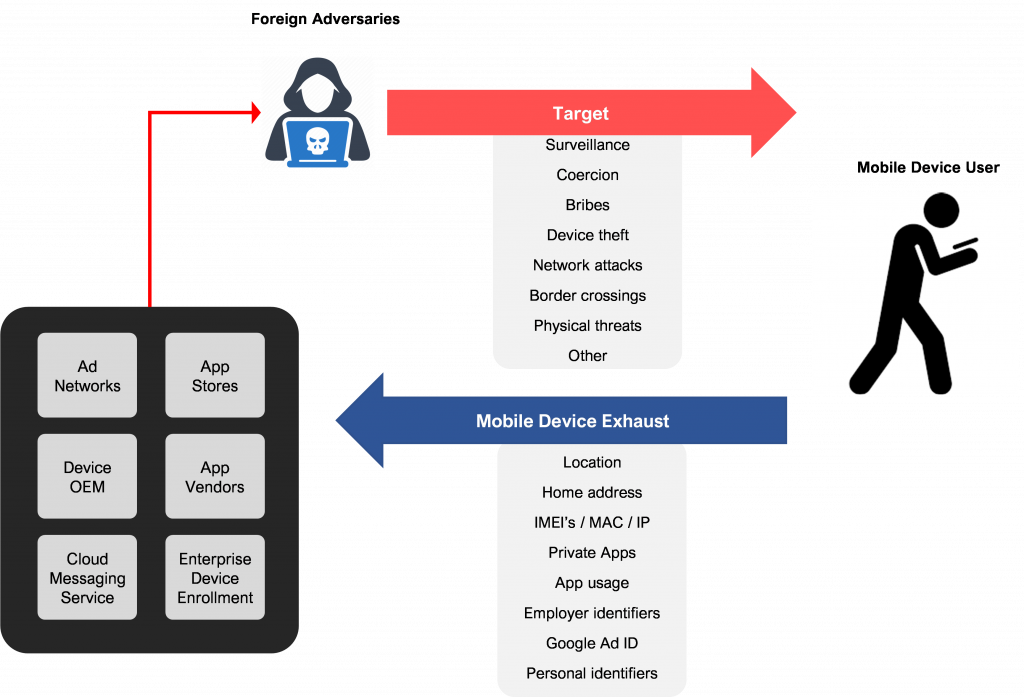
While the abuse of location data collected from mobile devices is a very valid concern, many government customers view the mobile data exhaust exposure more broadly and need to implement effective mitigations across hundreds or thousands of mobile devices.
As a result, we note the following limitations to the above:
- Disabling location services only limits access to location data by apps. Operating system services may still be collecting and transmitting location data,
- The recommendations are difficult to implement and operationalize[1],
- Many users and apps rely on features disabled by such mitigations, and
- Mobile data exhaust is broader than location data and includes personal identifiers, employer details (via enterprise enrollment services), private app use and frequency of use, fixed device identifiers such as IMEI’s and device serial numbers. All are very valuable to a foreign adversary for profiling and targeting government mobile devices and users.
Mitigating the risks associated with mobile data exhaust is a challenging technical and operational problem when relying on:
- Mobile operating systems designed for consumer monetization, and
- Management systems designed for enterprises that do not face the same threats as government agencies.
CIS Secure is working to address the risks by directing our efforts to educate our customers and mobile security certification entities on the threat.
We have also implemented extensive data exhaust mitigations in our altOS mobile cybersecurity platform developed specifically for government users. These include:
- Geo-locked modes of device operation to limit data exhaust in the vicinity of sites of interest to adversaries and covert sites,
- Policy controlled AD Id reset and other settings to limit data exhaust, and
- Private cloud messaging, app installation, device enrollment, and FOTA services.
CIS Secure works with government agencies, defense contractors, and others to better understands their mobile use cases and broader security requirements, including risks that arise from mobile device data exhaust. Contact us to learn more about CIS Secure, the altOS mobile security platfhttps://cissecure.com/contact-sales/orm, and our mission.
[1] For example, the NSA notes that the user should disable Wi-Fi/Bluetooth via the Settings app on IOS devices as the features in the control center may not work as expected.
